Cloud Workload Protection Platform (CWPP)
Security for VMs, containers, and Kubernetes without the high operational costs of agents
The Challenge
Agents Don’t Scale: Security Starts with 100% Coverage
Agent-based CWPPs require tedious deployments and management for each workload, leading to high TCO. Vendors offering a choice between agents and agentless approaches only add to the complexity and often have hidden limits on their ‘agentless’ capabilities. In addition, CWPPs only cover cloud workloads and miss risks in the cloud control plane, such as misconfigurations and overly permissive identities.
Partial deployment of agents causes serious blind spots.
IT teams need to spend countless hours installing, configuring, and maintaining agents.
Agents and network scanners have a significant performance impact and can be a security risk.
Security teams often need to burden development and DevOps teams to install agents, creating organizational friction.
CWPPs don’t have insight into cloud configurations and identities, leaving important security gaps.
Our Approach
Complete Cloud Security Without Agents
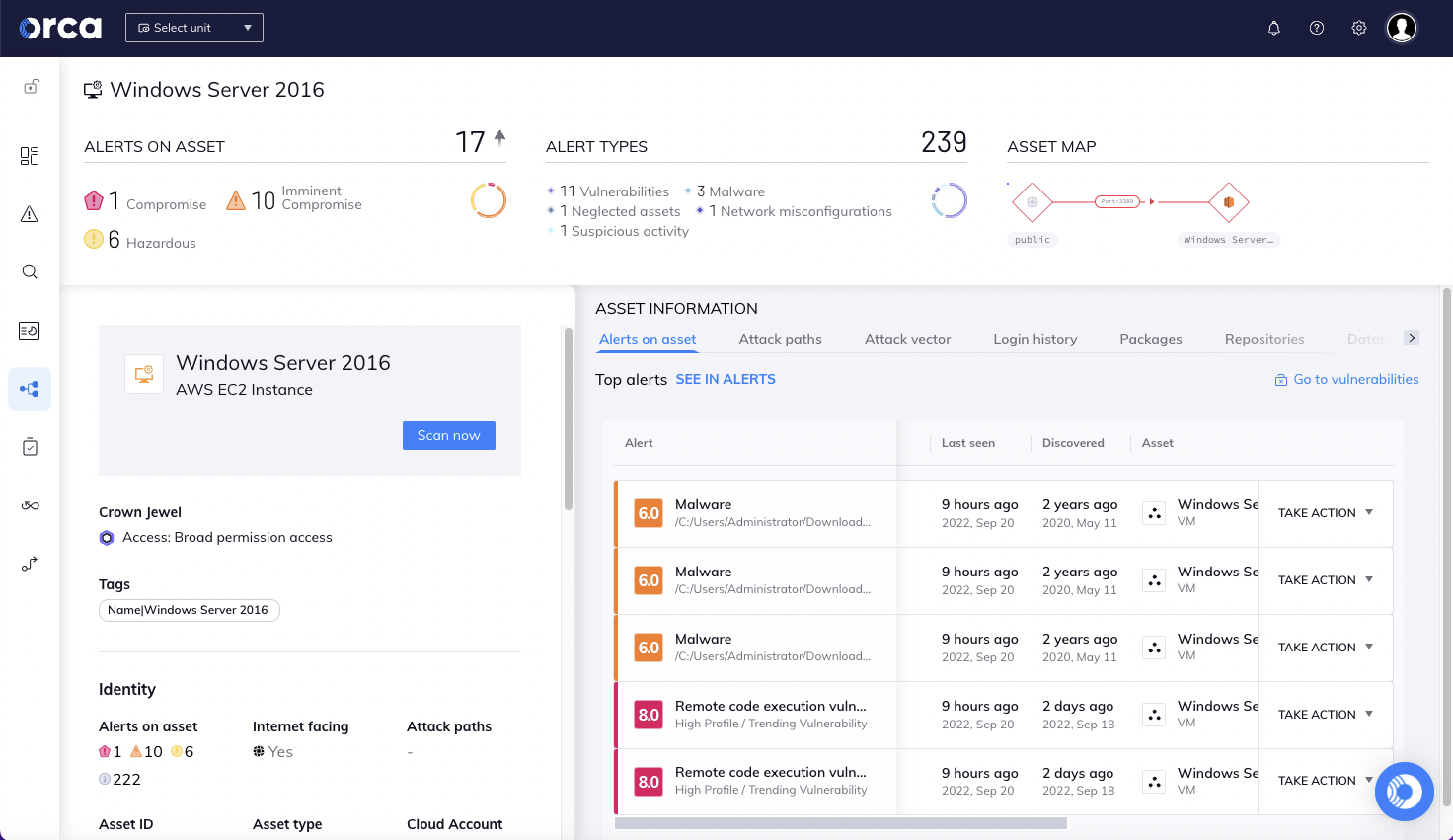
Unlike other CWPPs, Orca is completely agentless to fully deploy in minutes with 100% coverage, and includes wide and deep visibility into risks across every layer of your cloud estate, including cloud configurations as well as workloads. Orca combines all this information in a Unified Data Model to effectively prioritize risks and recognize when seemingly unrelated issues can be combined to create dangerous attack paths.
Orca collects data directly from your cloud configuration and the workload’s runtime block storage out-of-band.
Within minutes, Orca finds and prioritizes your most critical cloud risks, including vulnerabilities, malware, misconfigurations, lateral movement risks, IAM risks, and sensitive data at risk.
Unlike other solutions, Orca combines workload-deep intelligence with cloud configuration metadata all in one platform.
Orca’s patented SideScanning™ technology is a radical new approach that addresses the shortcomings of traditional agent-first cloud security solutions.
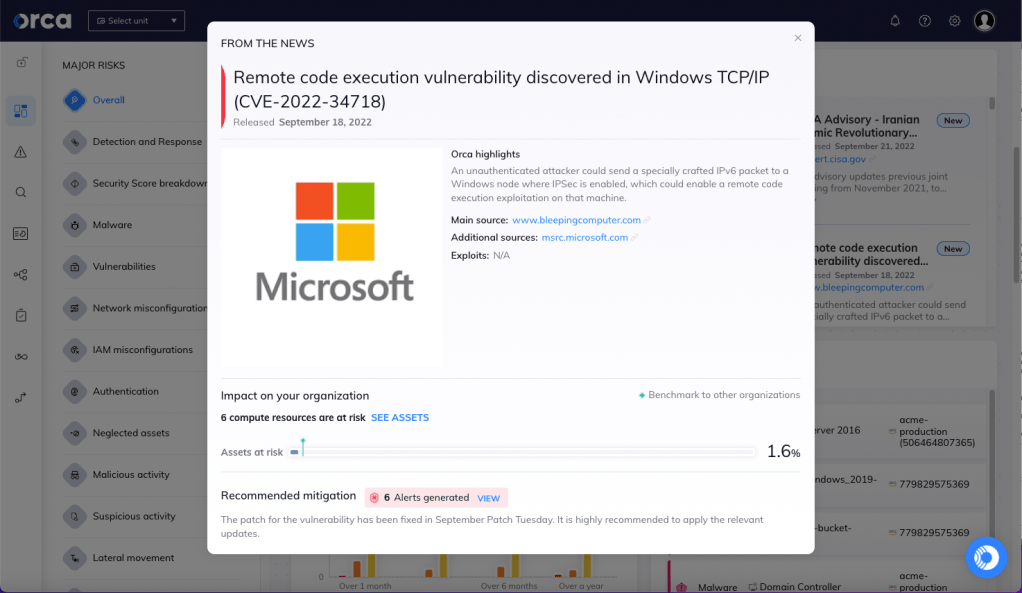
Cloud native vulnerability management
Orca creates a full inventory of your cloud environment and leverages 20+ vulnerability data sources to discover and prioritize vulnerabilities across your entire cloud estate.
- Orca’s workload inventory includes information on OS packages, applications, libraries, as well as versions and other identifying characteristics.
- Unlike other solutions that simply report on the CVSS score, Orca considers the context of cloud assets, their connections and risks, to understand which vulnerabilities need to be addressed first.
- In rapid response situations such as Log4Shell, Orca allows you to quickly identify vulnerable cloud assets and prioritize patching the ones that pose the greatest risk to the business.
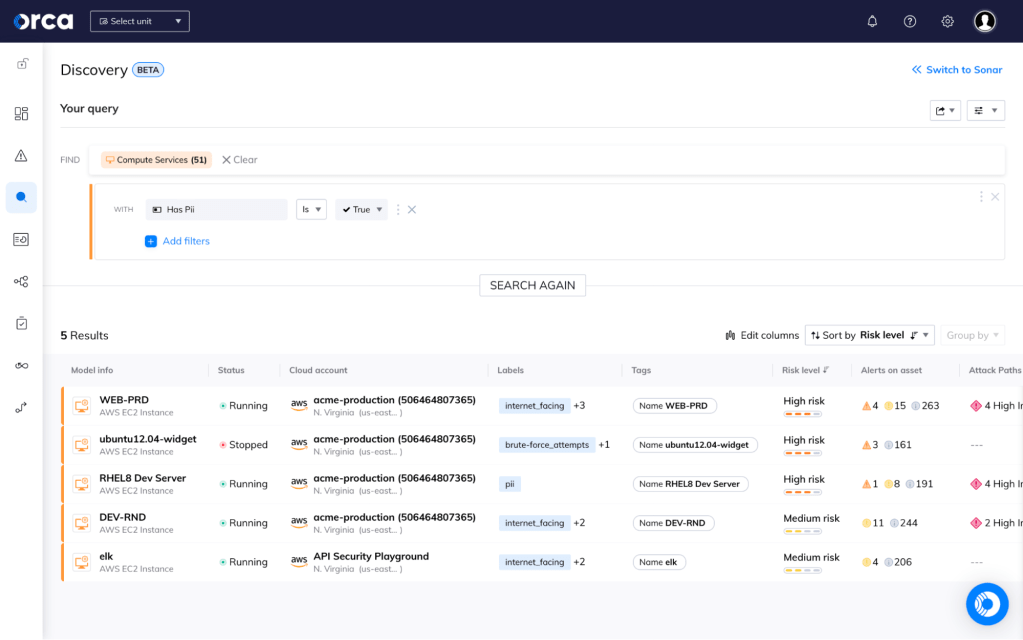
Protect your sensitive data with CWPP coverage
Orca scans the hidden corners of your cloud estate, searching for at-risk sensitive data, from personally identifiable information (PII) to protected healthcare information, and more.
- Detect at-risk sensitive data on every workload across your cloud estate regardless of whether the assets are running, idle, paused, or stopped.
- Sensitive data detection includes PII, including physical addresses, email addresses, credit card numbers, and Social Security identifiers.
- Understand which risk combinations are a straight attack path to your crown jewels.
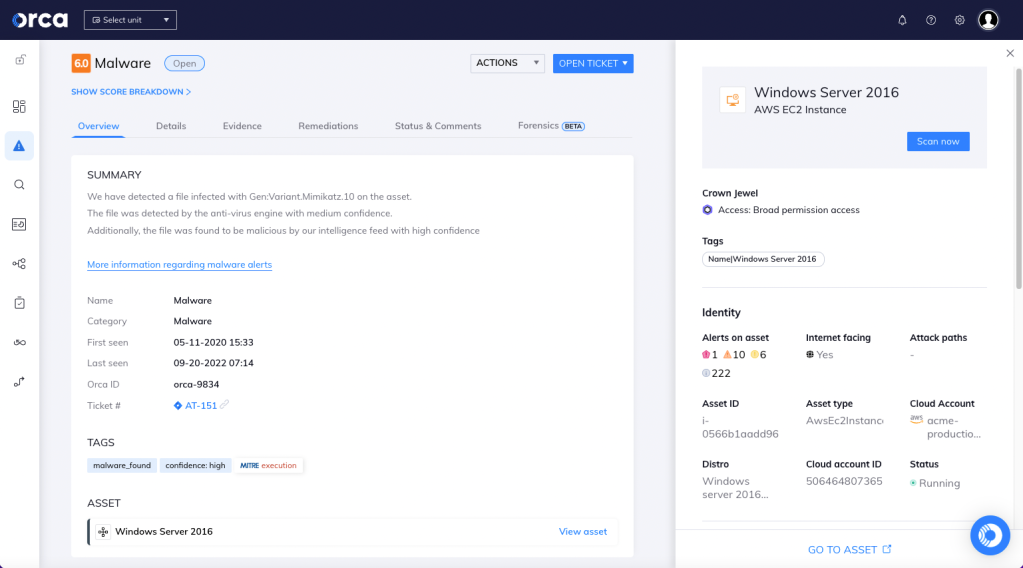
Detect known and unknown malware
Orca uses extensive malware detection techniques to locate known and potentially malicious code in your cloud workloads and resources.
- Signature-based scanning checks for file hashes of known malware.
- Heuristic file analysis closely inspects files to determine their purpose, destination, and intent.
- Dynamic scanning executes a file in a controlled virtual environment to observe its actions.
- Genetic signature detection uses previous malware definitions to discover malware within the same family.